Don't pay an SSO tax to log in with your own IdP
The standard SaaS pattern is to put SSO behind an "Enterprise+" tier and price the privilege of using your own identity provider as a multiplier on the contract. The alternative most platforms offer is no SSO at all, or a basic OAuth-only login that does not satisfy your IT review.
Vendure ships SSO in the Platform bundle, supports both SAML 2.0 and OIDC, and integrates with the identity provider your organisation has already standardised on. Procurement evaluators can stop comparing licence multipliers.
Both protocols, named providers, real lifecycle hooks
One plugin that covers the full SSO surface your IT review and implementation team need.
SAML 2.0 and OIDC, both first-class
Configure SAML 2.0 and OIDC providers side by side under a single plugin. OIDC discovery is automatic; SAML accepts an IdP metadata URL or explicit endpoint and certificate values. Sessions are hardened with CSRF state tokens and configurable timeouts.
Named IdP support
Any standards-compliant SAML 2.0 or OIDC provider works. We run regularly against Okta, Microsoft Entra ID, Google Workspace, Auth0, Keycloak, OneLogin, PingIdentity, Microsoft ADFS, and Shibboleth. No vendor-specific dialects, no lock-in to one IdP's flavour of either protocol.
Auto-provision and role mapping
On first successful SSO login, Vendure provisions the admin account from the verified IdP assertion. IdP groups or claims map to Vendure roles through a pluggable strategy, with a safe default for unmapped users. Deprovisioning stays in the IdP, where your IT team already manages joiner-mover-leaver.
Claim and attribute mapping
Every IdP emits a slightly different schema. Vendure lets you map email, first name, last name, and role claims per provider, so each connection lines up with what the IdP actually sends. Multiple providers can run in parallel with independent mappings, useful when a parent and an acquired business haven't consolidated identity yet.
The auth flow you would draw on a whiteboard
OIDC: Admin clicks SSO login → Vendure redirects to your IdP with a state token → IdP authenticates and returns an auth code → Vendure exchanges the code, fetches userinfo, and creates the session.
SAML: Admin clicks SSO login → Vendure issues an AuthnRequest → IdP POSTs a SAMLResponse to the Assertion Consumer Service → plugin validates the signature → session created.
Callback URLs are predictable: /sso/callback/{providerId} for OIDC, /sso/metadata/{providerId} for the SP metadata you hand to your IdP team. Both prefixes are configurable via callbackPathPrefix.
Two implementation shapes this plugin was built for
SSO is a baseline requirement for enterprise IT. The shape of the implementation differs across organisations.
SSO is one of three plugins that make up the admin governance story
SSO answers who is logged in. Audit logging records what they did: every login success and failure, every entity create and update, and optionally every read. Row-level access control scopes what their queries return, per administrator, per request.
You configure each plugin independently. The actor identity that SSO produces flows through every request automatically, so audit entries and access-control filters pick it up without any plumbing on your side. Together they're the three pieces your security team is asking about when they say governance and compliance.
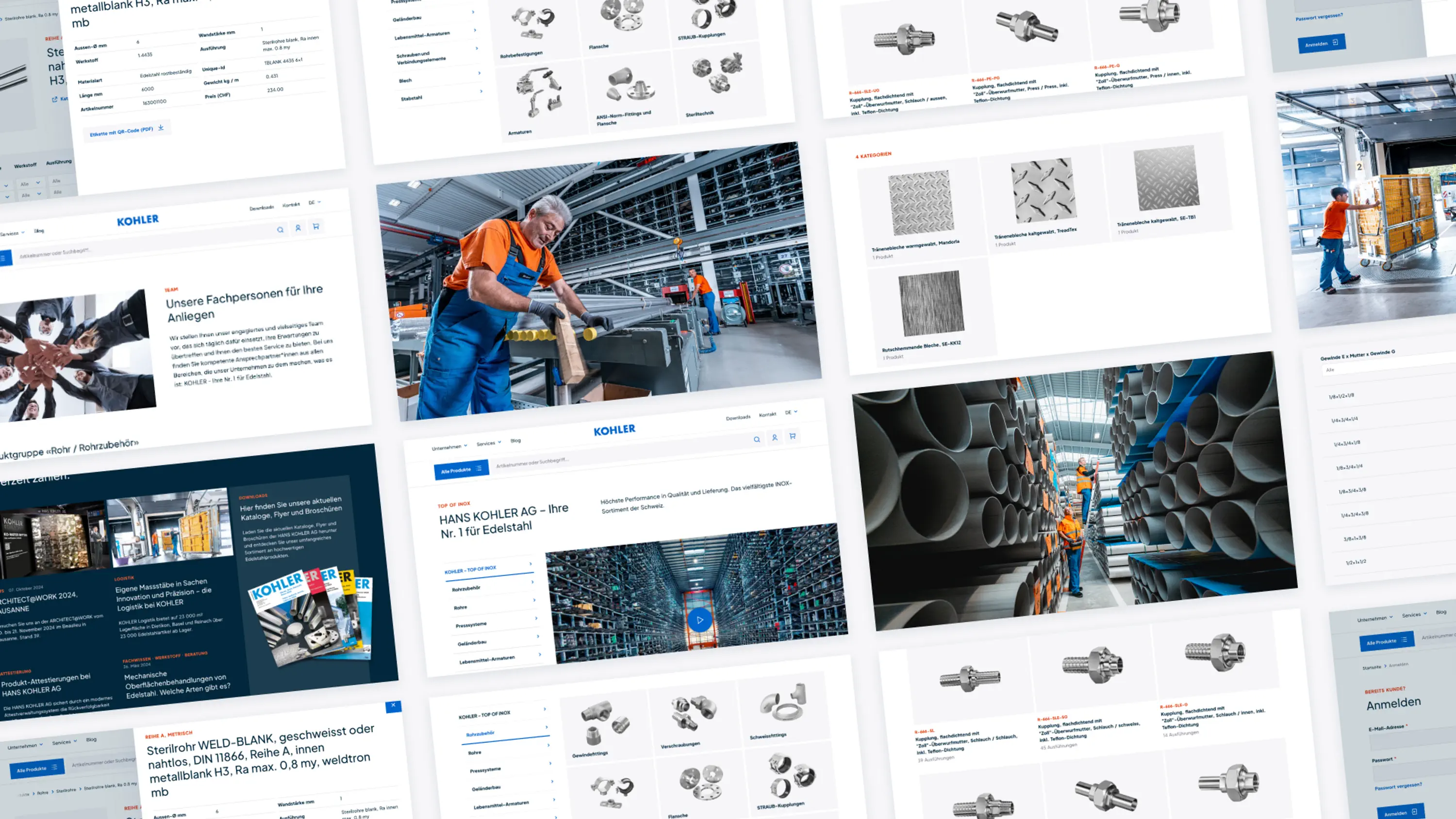
Trusted by complex B2B commerce and enterprise retail.






What IT and security teams ask about Vendure SSO
The procurement-gate and implementation questions that come up in every SSO evaluation.